This article is sourced from Chainalysis and translated by Christina for Odaily Planet Daily.
Surveys indicate that in 2019, 18% of Americans and 35% of American millennials had purchased cryptocurrency, reflecting growing public acceptance of digital assets.
Mainstream financial institutions like JPMorgan Chase are entering the space, and major retailers such as Amazon and Starbucks now accept BTC payments. However, the decentralized and semi-anonymous nature of cryptocurrency also makes it uniquely attractive to criminals. In recent years, dark web markets have increasingly relied on BTC and other cryptocurrencies to facilitate payments for illegal goods and services—including firearms, narcotics, and stolen personal data—effectively turning these platforms into "lawless zones" and safe havens for illicit activity.
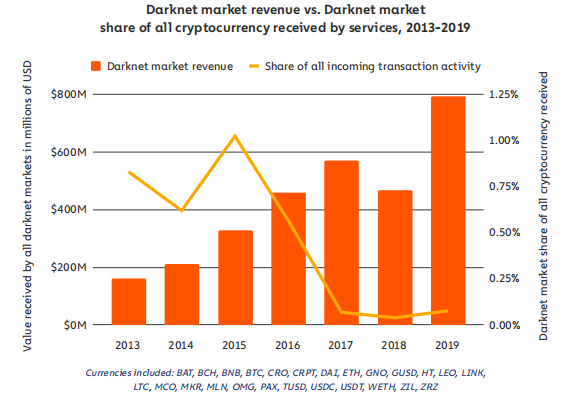
Data shows that after a slight dip in 2018, total sales on dark web markets surged by 70% in 2019, surpassing $600 million for the first time. Moreover, since 2015, the share of all cryptocurrency transactions linked to dark web markets has doubled—rising from 0.04% to 0.08% in 2019.
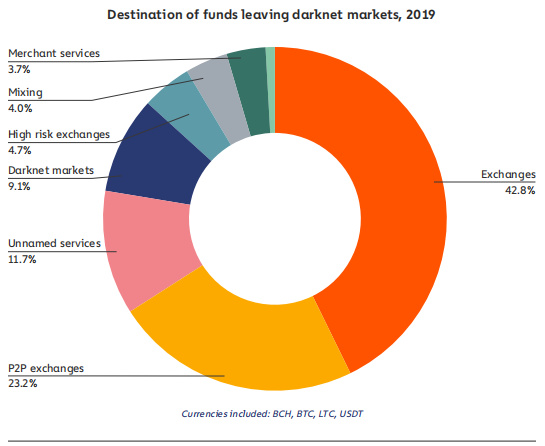
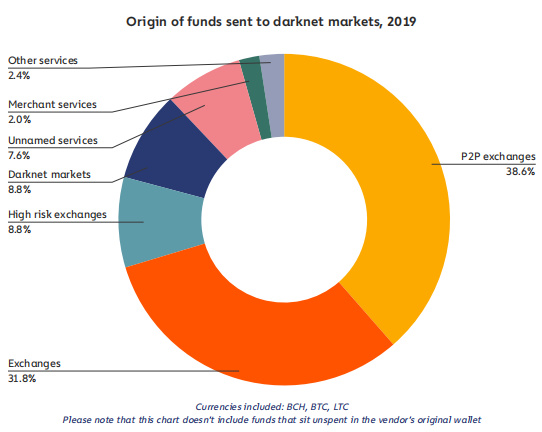
As in past years, the vast majority of dark web transactions are still conducted through cryptocurrency exchanges, which remain the most common service customers use to send funds to vendors.
Although dark web transactions still represent a tiny fraction (0.08%) of overall cryptocurrency activity, their volume has grown significantly amid a recent resurgence in dark web markets—even under increased law enforcement scrutiny.
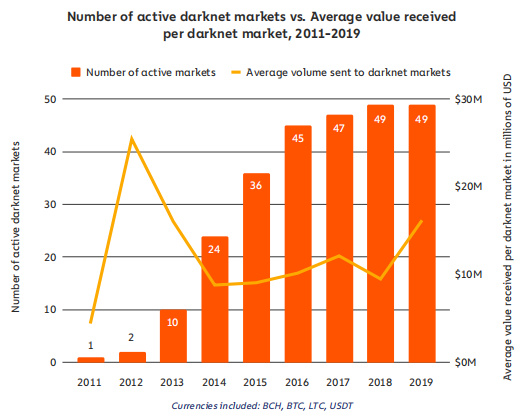
While eight of the 49 active dark web markets from 2018 shut down in 2019, eight new ones emerged that same year. Overall, excluding the peak years of Silk Road (2012–2013), each active dark web market generated higher revenue in 2019 than in any previous year. This trend occurred because when some markets closed, others proved capable of absorbing the displaced demand and meeting customer needs.
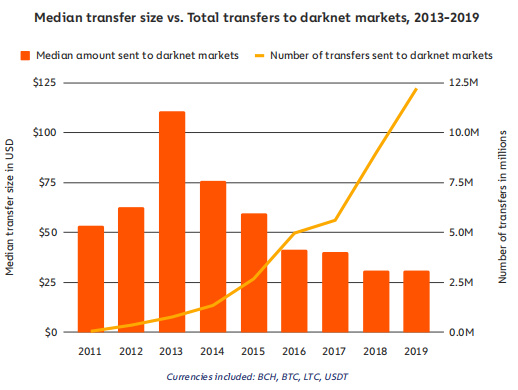
The data also confirms that revenue growth was driven primarily by an increase in the number of purchases, not by larger individual transactions. The median purchase size in USD remained relatively stable, while the number of cross-market transfers jumped from 9 million to 12 million. This suggests that either more customers were buying from dark web markets in 2019, or existing customers were making more frequent or larger purchases.
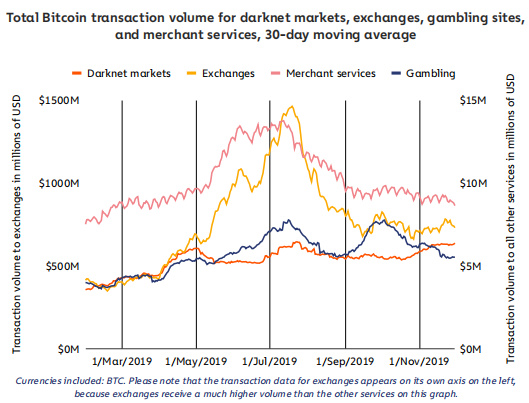
Interestingly, dark web market activity appears less sensitive to cryptocurrency price swings or other seasonal volatility compared to other services. The chart above compares Bitcoin transaction volumes across dark web markets and three other service categories throughout 2019; dark web markets show significantly smaller spikes. Over the entire year, activity on these markets remained within a much narrower range of transaction volumes, suggesting customer behavior is relatively insulated from BTC price fluctuations.
Drugs Still Dominate the Dark Web
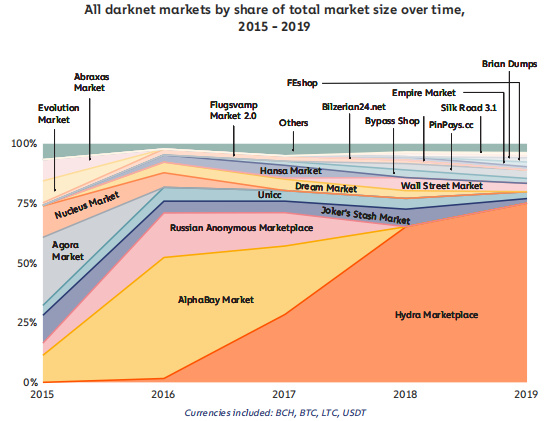
As the chart above illustrates, dark web markets have evolved over time, with drug-related listings consistently dominating. It's worth noting that some of the top markets listed serve only specific countries or regions. For example, Hydra Marketplace—the most popular market shown—is exclusively available to Russian customers. The chart below presents an alternative view, focusing only on markets with a global customer base. While certain markets may be more popular in some countries than others, the following data is generally more relevant to investigators in the U.S. and Western Europe.
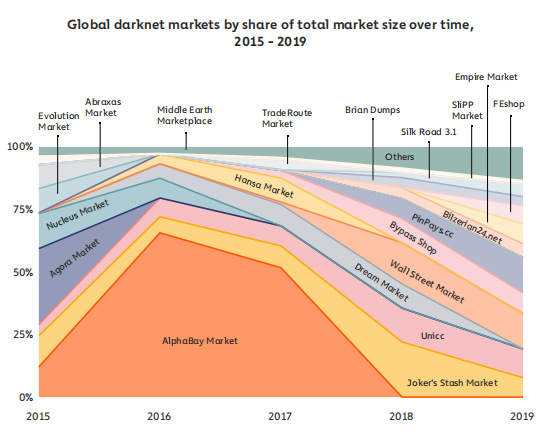
Drug markets continue to dominate here as well. However, markets specializing in other illicit goods also generate substantial revenue. Joker’s Stash Market and UNICC stand out as two of the most consistently popular markets throughout the entire observation period.
Fighting Cybercrime: Should Law Enforcement Target Vendors—or Shut Down Markets?
For a long time, law enforcement strategy has focused on dismantling dark web markets. On the surface, this seems logical: if you can eliminate all vendors at once, why pursue individuals? Following this approach, agencies scored major victories by shutting down prominent markets like AlphaBay and Hansa. Yet the problem is that when one market closes, others quickly fill the void. By the end of 2019, at least 49 active dark web markets existed, offering users and vendors plenty of alternatives. Moreover, they can easily discover new markets on forums like "Dread."
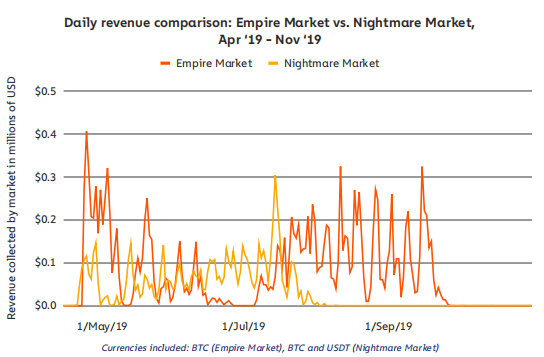
Take Nightmare Market—a short-lived, moderately popular platform that shut down on July 23, 2019. Unlike other cases, Nightmare wasn't taken down by law enforcement. The exact cause remains unclear, but users began fleeing en masse after July 23. By month's end, trading activity on Nightmare had nearly ceased. As the data shows, Empire absorbed much of Nightmare's former business, with its sales spiking precisely as Nightmare's declined.
The closure of Nightmare Market highlights the broader challenge facing dark web enforcement. With so many alternatives available—and vendors able to easily notify their top customers where they've relocated—it's no wonder many law enforcement agencies have shifted their focus toward arresting individual vendors.
Below is a related case study. We interviewed Stefan Kalman, a user analyst and narcotics investigator with the Swedish Police, whose work focuses on dark web markets.
In 2014, Swedish police officer Stefan Kalman and his team identified a dark web vendor operating under the alias "Malvax" on both Silk Road 2.0 and Evolution. By monitoring his activity on Silk Road forums, they discovered he was also selling on two other dark web markets—Evolution and Flugsvamp—which catered specifically to a Swedish audience. Malvax listed over 280 products for sale, including the potent synthetic opioid fentanyl. While police had intercepted some of his shipments—identified by labels from PostNord, Denmark's leading private courier—his real identity remained a mystery.
Malvax employed sophisticated obfuscation techniques and operational security to hide his tracks. However, a breakthrough came in 2015. After the FBI shut down Silk Road 2.0's servers in late 2014, investigators seized the hardware. By analyzing server logs, they uncovered several Bitcoin addresses linked to the Malvax alias. Tracing these addresses led them to a regulated cryptocurrency exchange based in the UK.
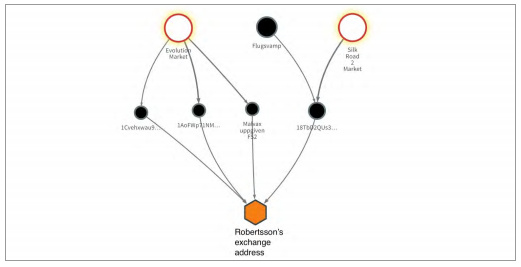
Stefan's team served the exchange with a subpoena. The information provided was enough to unmask Malvax as Fredrik Robertsson.
To confirm Robertsson was still active, the team made a covert purchase from him on Flugsvamp. With judicial approval, they then wiretapped his phone, placed a GPS tracker on his car, and set up surveillance cameras at his residence—all while placing additional test orders and monitoring his online and offline behavior.
The evidence gathered by Stefan's team against Robertsson and his brother led to their conviction in Swedish courts for narcotics trafficking on the dark web.
Deep Dive: Carding Stores
While drug marketplaces dominate the dark web, they aren't the only operations generating consistent revenue. Let's look at another prevalent category: carding stores.
You've likely heard of massive data breaches at companies like Capital One and Home Depot, where tens of millions of credit card details were stolen. Ever wonder where that data ends up? A significant portion flows into carding stores—dark web marketplaces where users buy stolen credit card information.
Take UNICC as an example:
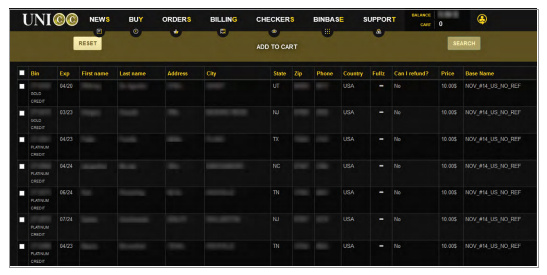
The image above shows a sample listing from UNICC. Prices per card range from $2 to $15, averaging around $10. The final price depends on several factors. One is geography: cards issued in the U.S. and Western Europe typically cost more. Another key factor is whether the listing includes personally identifiable information (PII) like a street address and phone number. Since most online merchants require this PII for verification, its inclusion significantly boosts a card's value.
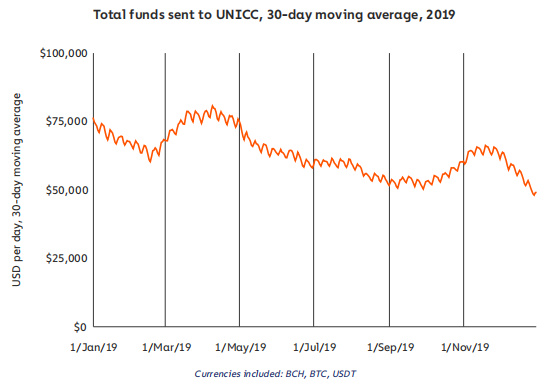
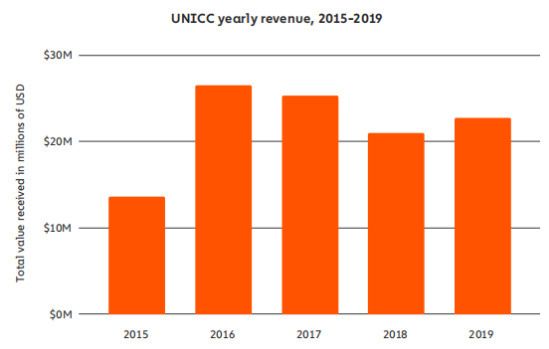
In 2019, UNICC received at least $22.7 million worth of cryptocurrency, ranking it as the fourth most active dark web marketplace that year. Its activity remained relatively stable, peaking in April. Based on its total sales volume and an estimated average card price of $10, UNICC likely sold stolen data for nearly 3 million individuals.
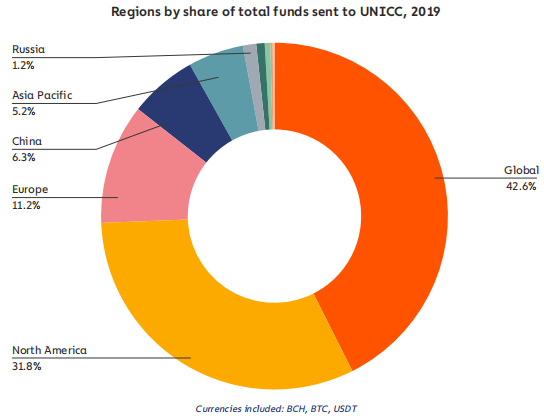
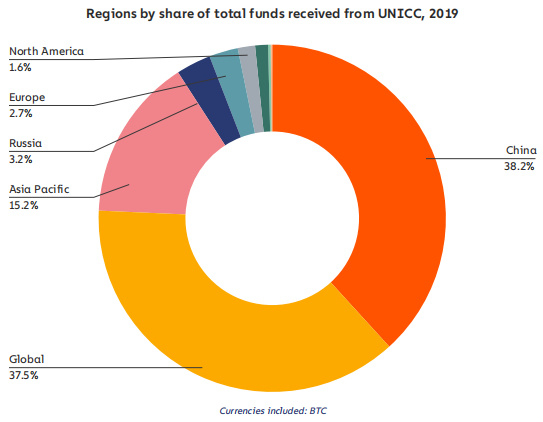
Regional data indicates that most buyers on UNICC were located in North America (second only to the "Global" category), while the majority of sellers were based in China.
What’s Next for Dark Web Markets?
Dark web markets are evolving with new security features. Many now use multisignature technology, requiring both buyer and seller to confirm an order before funds are released. Another innovation is walletless escrow, or direct deposit, where each transaction generates a unique, one-time wallet, and the buyer's cryptocurrency is sent directly to the seller.
Some platforms are also adopting new infrastructure to avoid law enforcement takedowns. OpenBazaar, for instance, uses a fully decentralized architecture—similar to blockchain or the Tor browser—where users simply run a program to connect peer-to-peer, eliminating the need for a central website.
Furthermore, an increasing number of dark web markets now accept—or even require—privacy-focused cryptocurrencies like Monero (XMR). Monero's obfuscated public ledger makes it substantially more difficult to trace senders, recipients, or transaction amounts.
